*uopeasy (THM)
Gray box penetration test
TryHackMe – uopeasy Write-Up
topics: Web application security, SQL injection, Wordpress R.C.E, php reverse shell, cracking hashes
Enumeration
Local Privilege Escalation
Root Privilege Escalation
tools: nmapAutomator, dirsearch, wpscan, johntheripper
attempted to use for practice with manual SQLI but it is time based.
Enumeration
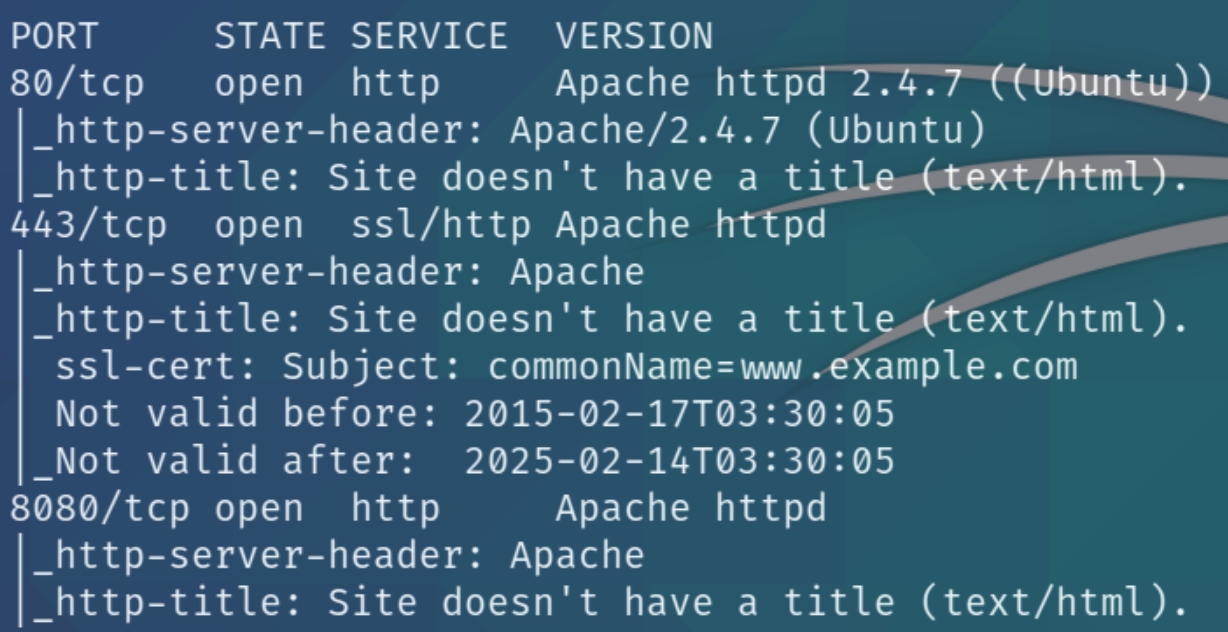
initial nmap scan ../.autonmap.sh $ip Full
We have three ports open, two HTTP and one HTTPS. As this is a gray box test, we're aware that we'll be targeting a Wordpress site and performing SQL injection to retrieve credentials from the server database. Let's navigate to the homepage of each port.
80
It's safe to assume that this might not be the way in but let's run a dirsearch scan anyway
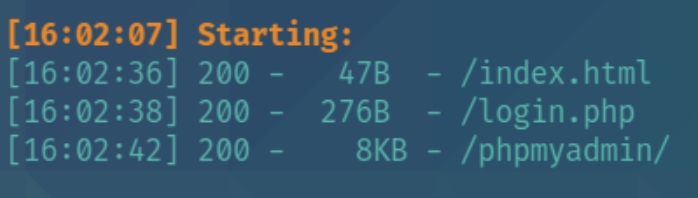
python3 dirsearch.py -u $ip -e php,html,txt
From dirsearch we can see there are 2 hidden directories, login.php and phpmyadmin. As we know that we'll have to perform an SQL injection lets run a brute force attack on the login page to check for valid credentials.
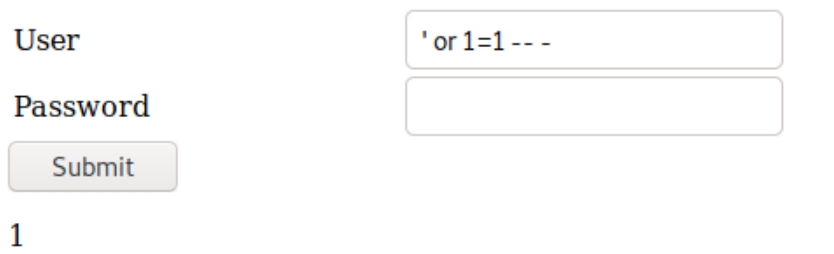
I was unable to input a blank password using hydra and retrieve valid credentials, so I tested generic SQLi terms and found the following
When incorrect credentials are inputted, a zero is returned in contrast to a one as shown above. This confirms that the login page is vulnerable but we don't yet have the proper syntax to dump credentials.
As this is MySQL syntax, we can attempt error-based SQLi.
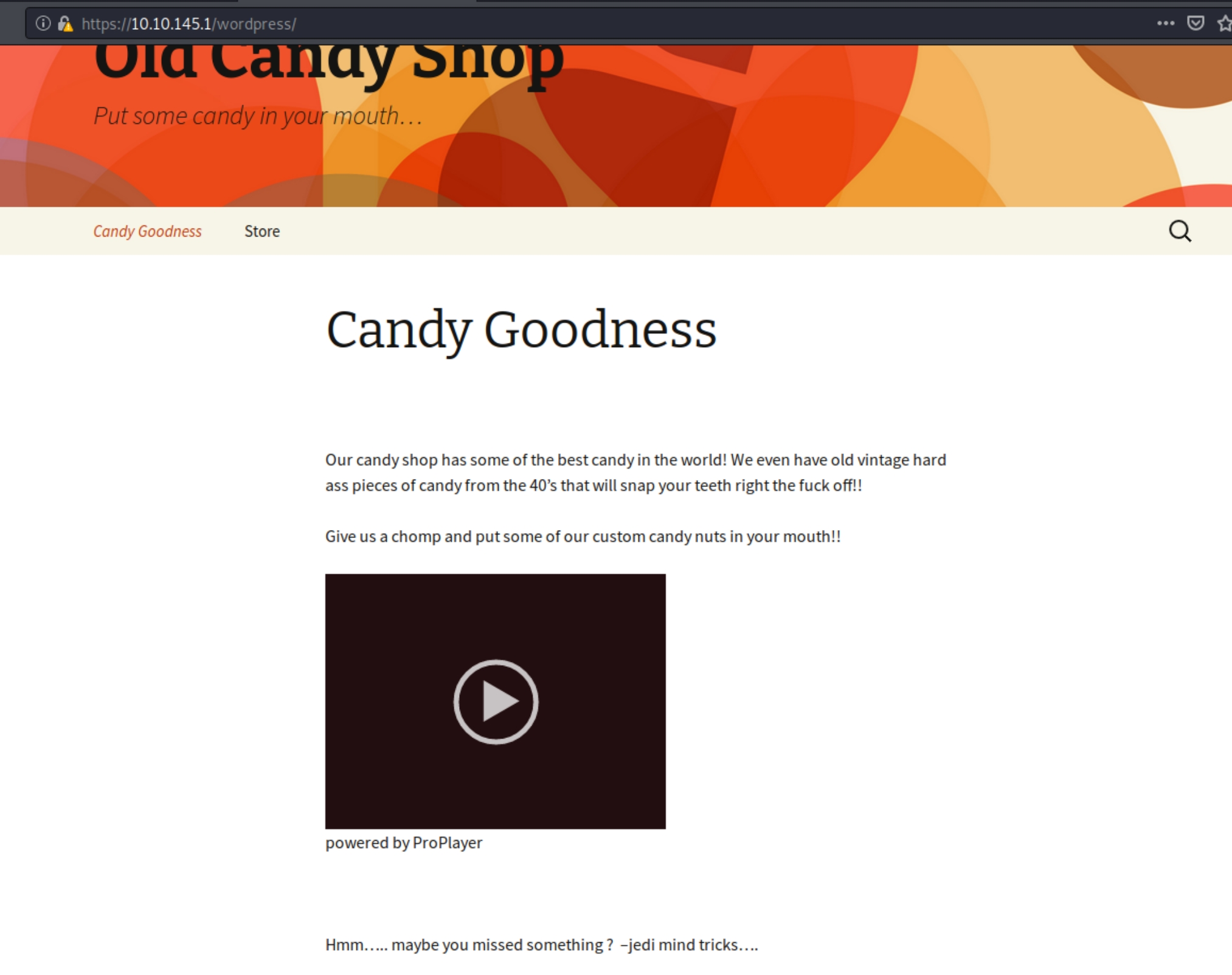
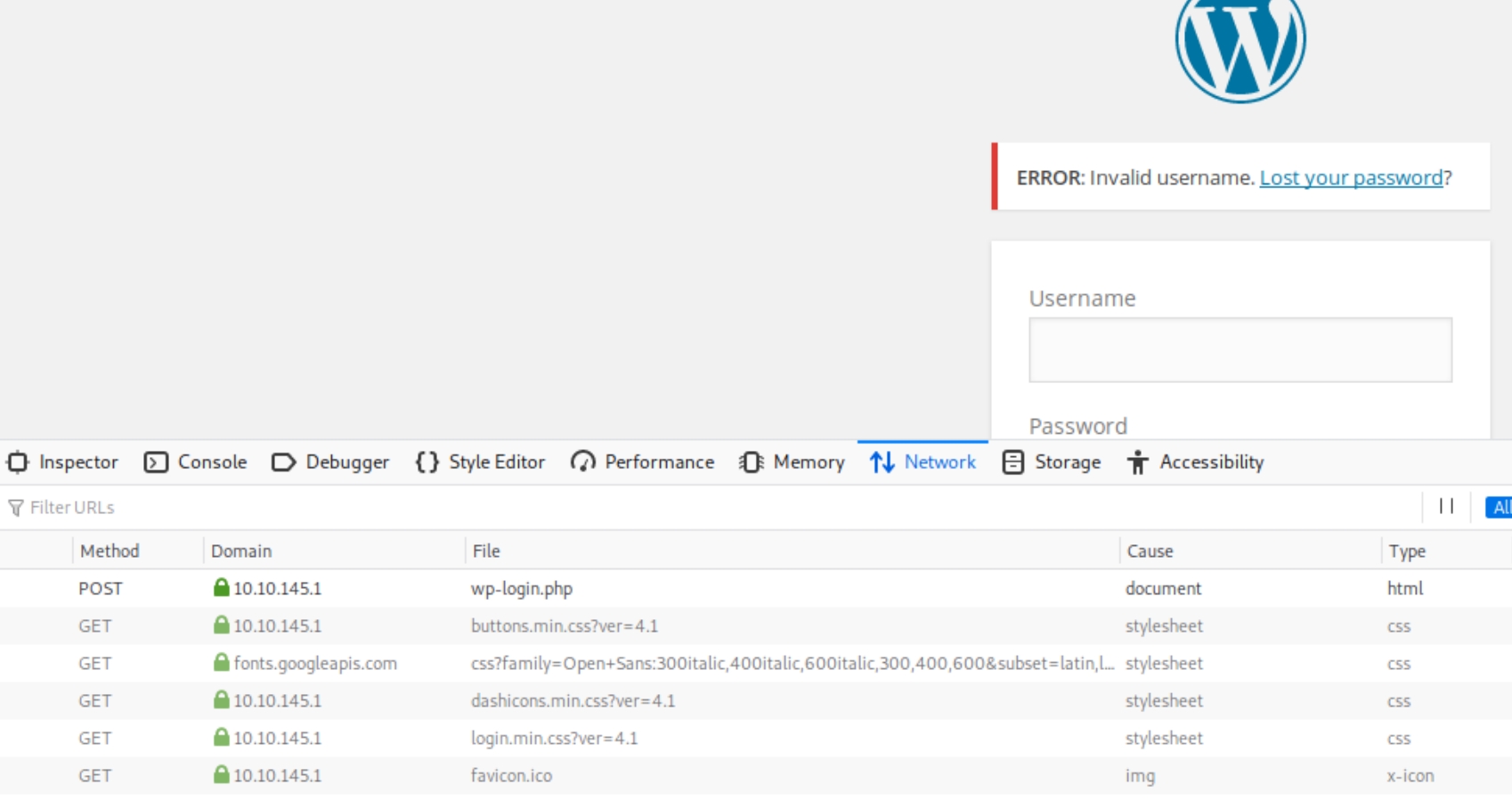
443/8080
These ports share the same homepage that leads to the directory http://$IP/wordpress
We have a store subdirectory containing elements such as the cart, checkout, and receipt, we also have a section at the bottom of the site for posting comments. The room told us to achieve initial access through SQL injection, we'll have to identify a place to test for this. Lets run an nmap vulnerability script scan
w
w
hydra -L genericSQLi.txt -p test 10.10.101.254 http-post-form "/login.php:user=^USER^&password=^PASS^&Submit=s:0"
Local Privilege Escalation
Root Privilege Escalation
Last updated